This the another in a (possibly never ending) series of examinations into the various types of attacks and scams in the crypto world. If this piece is helpful to you, please let me know on twitter: @CryptoCoinBen.
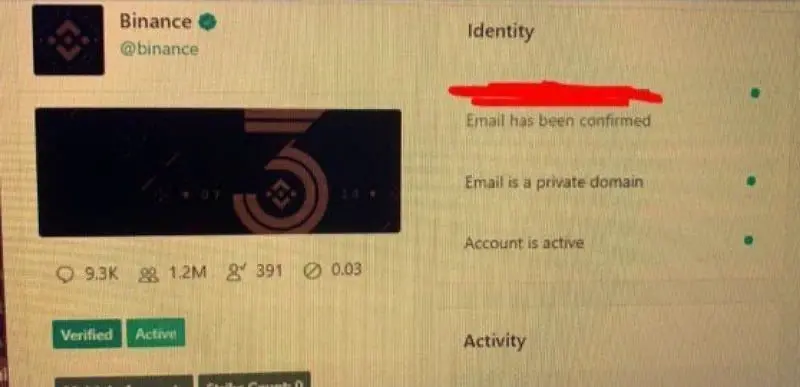
This morning hundreds of celebrities, politicians, businessmen and crypto influencers began posting requests for Bitcoin. All of them using the current global pandemic theme and ‘offering to give back’, or ‘partnering with cryptoforhealth’.
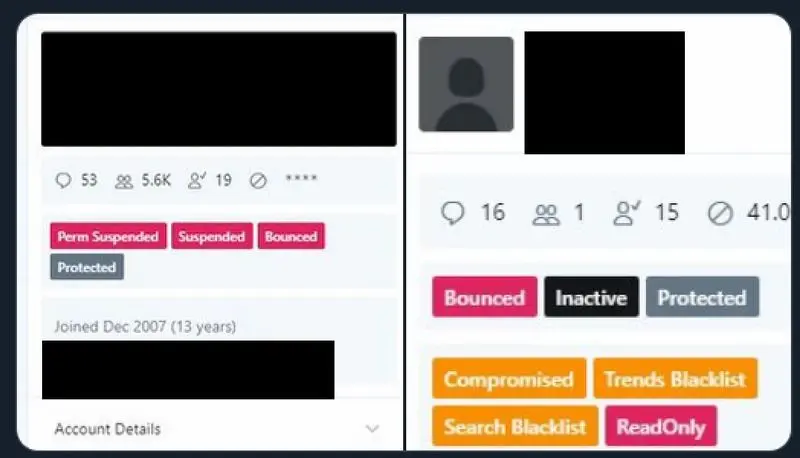
At this stage, the reaction from Twitter has been swift. They have limited the spread of this scam and appear to have limited the attackers to around 100 accounts and ‘just’ a couple of hundred thousand dollars. Given the breadth of the attack, the access to these account and/or the 0-day needed to execute something like this would have been worth significantly more.
Lets take a look at what this all means.
What was the message that was spread?
Initially, the attacker used popular accounts to spread messages offering to double any Bitcoin that was sent to them.
I’m feeling generous because of Covid-19.
I’ll double any BTC payment sent to my BTC address for the next hour. Goodluck, and stay safe out there!
{{ BTC WALLET ADDRESS }}
This is pretty typical for the social engineering attacks going around at the moment.
- It plays on the current global threat. Hundreds of thousands of domain names have been registered in the last 6 months that specifically target the COVID-19 pandemic.
- It creates FOMO, a call-to-action with a deadline. It encourages people to act quickly, without thinking about it too deeply.
- It is apparently sent from a reputable sender. Someone who is trusted and recognised by the recipient.
Who sent it?
We don’t know. Given the number of victim accounts used, it is safe to assume it was someone with insider access, or knowledge of an unpublished vulnerability (0-day). A 0-day of this size would be worth up to a million dollars on the black market, or just a few thousand from Twitters bug bounty program.
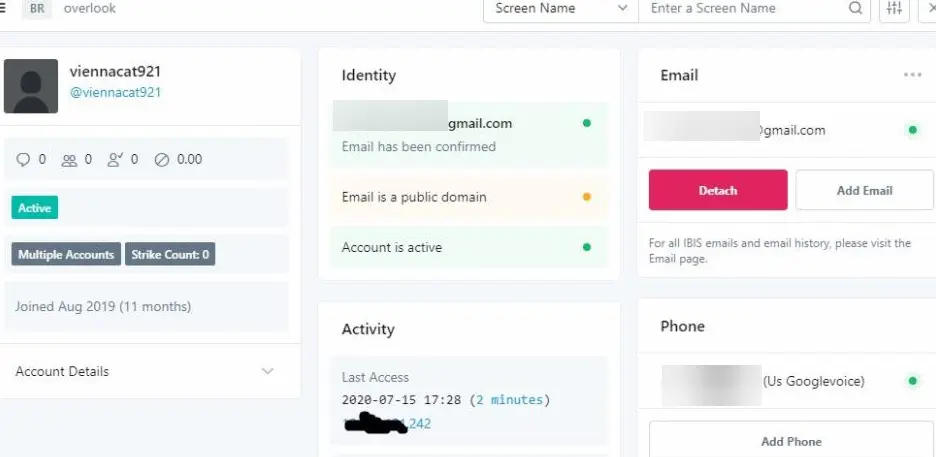
How did they manage to get access to so many accounts?
The simple answer may be a vulnerability in Twitters security. This is both the technical security controls on the website, as well as the people. Twitter take security extremely seriously and a breach of this size should not have gone unnoticed.
It may have been an inside administrator that was compromised. Either knowingly or unknowingly complicit, or perhaps in physical danger or threatened with reputational damage.
Occams razor states that the most likely source is a combination of these attack vectors. An internal administration panel or API maliciously used to make the post. Two question still remain:
- Internal or External threat actor.
- Official process, or an internal API/Admin vulnerability.
Of course there are other attack vectors as well. Such as the exploitation through a third party. It is possible all of these accounts were using the same:
- service/app to manage their social media.
- password manager to store their Twitter password
- phone OS and/or cloud storage provider (ala ’The Fappening‘)
… But this would rely on Multifactor Authentication (MFA) having been disabled on the account. Given the accounts exploited, I would be surprised if NONE of them had MFA enabled. EDIT: Confirmation that at least one of the affected accounts had MFA enabled
But with all of this access, why attempt a non-sophisticated Bitcoin scam?
UPDATE: Twitter have confirmed that someone was able to socially engineer their employees in order to gain access to the Twitter Admin Panel. Still unclear how this was done, or what type of access the attacker(s) had access to.
Why was it sent?
We don’t know this either. BUT, it seems unlikely to be just for the Bitcoin scammed. This 0-day would be worth more to sell, then to use in this manner. At the current time, it has ‘only’ raised a little over $100k through Bitcoin victims. This leaves a couple of options:
- State sponsored attack - In particular from North Korea, who have previously used this style of social engineering attack via email previously (and who can NOT receive bounties from American organisations).
- Political Statement - It is glaring that perhaps the most notorious account (the @RealDonaldTrump) was not used, nor were any of his close allies. Is this a ‘proof-of-compromise’ statement. Should we expect DM’s and other private information to be leaked or used as compromising material in extortion or blackmail attempts.
- Hacktivist - Those looking to make a statement or prove their skills against an opponent such as Twitter
- Diversion tactics - Twitter and the rest of the world are currently focused on this breach. Are there other activities going simultaneously?
Is it all bad?
For the Bitcoin community, there may be a silver lining to this attack? The term ‘Bitcoin’ has been broadcast to the largest audience ever. Aside from the billions of followers the compromised accounts have, it is also appearing in mainstream media news.
While it would have been preferable to have had a good news story, ‘there is no such thing as bad publicity’ apparently. Now is the time the crypto influencers should be promoting the benefits of crypto currencies.
For now, it also appears as though Twitter has stopped:
- Anybody with a blue checkmark from tweeting.
- Any tweets with a Bitcoin wallet address in it.
How to avoid this style of attack.
- Always assess the vendors that you use. Review their security posture and history.
- Always use Multifactor Authentication.
- Be mindful of the material you share online. If it is not your keys, it is not your … information.
- Be smart - If something sounds too good to be true, it probably is.
Editor-in Chief
Related Posts




Subscribe to our newsletter!
Information